- Author: Damon DiPietro
- Author: Jim Coats
One of the sad realities of email is that all of us will at some point be subject to "phishing" attempts. Wikipedia's definition of phishing is "the act of attempting to acquire information such as usernames, passwords, and credit card details by masquerading as a trustworthy entity in an electronic communication." Read on for important information you should know about the trusted institutions you work with online and about these phishing messages. These tips will help protect your personal information online and keep you from becoming the victim of a scam.
About your institutions... Banks, credit card companies, hospitals, universities, and other institutions have rigorous standards with regard to divulging personal information IN BOTH DIRECTIONS of the electronic communication—meaning that they won't send out your SSN, account password, etc. over email and they won't ask you to do so either. You will be directed to a secure website for any such request. So the first tip is this: Any electronic message that asks for personal information or account information over email is a phishing attempt! There were exceptions to this ten years ago, but I can't think of any today.
Sometimes the email is a little trickier and won't ask you to send the information over email but will direct you to a link contained in the email. Here are a few things to consider when judging the legitimacy of this kind of email:
1. How is the grammar, syntax, or vocabulary in the email? Many of these scams originate in other countries where English is not the first language or the particulars of American English aren't known. So look for misspelled words, incorrect or incoherent phrasing, or missing or bad punctuation.
2. Does the email comes with an "urgent" warning or a threat about your account if you do not take some action? If so, it is most likely a phishing attempt. The only exception to this is when the email includes contact information for the department that sent the message (usually a phone number or email address). When in doubt, call the sender and find out if the email is legitimate.
3. If you hold (but DO NOT CLICK!) the mouse over the link that you're being told to use to "fix" your problem, you can see the actual address it will go to. Many times it will not be an address having to do with the institution that supposedly sent the message. For example, if you were to receive an email from UC Davis saying they're migrating servers and your account will be closed unless you click on the link, and then you moused over the link and it said something like "http://apohome.yuca.uk," that's obviously not a UC Davis website!!
I hope these tips are helpful. There are many more clues that can give away these phishing attempts, but these are the basic ones. Please send this information on to anyone who has questions about phishing attempts or has ever fallen for one.

- Author: Dave Krause
The web team transitioned the majority of our web applications and sites to ucanr.edu today. The ANR Portal, Site Builder, Collaborative Tools, and most other applications will now show ucanr.edu instead of ucanr.org. Here are few links demonstrating the new URL:
- Portal - http://ucanr.edu/portal
- Site Builder - http://ucanr.edu/sb3
- Collaborative Tools - http://ucanr.edu/collaborate
- File Vault - http://ucanr.edu/filevault
- Master Gardener VMS - http://ucanr.edu/mg
All old links to ANR web tools should redirect to the new URL. If you see 'ucanr.org' in your address bar or have trouble accessing a tool, please log out of the portal and log back in.
Additionally, all Cooperative Extension sites running under Site Builder have been moved to ucanr.edu. For example, http://ceyolo.ucdavis.edu is now http://ceyolo.ucanr.edu. Please note, the old urls will continue to function; however, once you are in a site, the navigation links should reflect the new URL.
All standard Site Builder URLs have also changed to ucanr.edu. Any site with http://ucanr.org/sites/sitename will now have http://ucanr.edu/sites/sitename as the primary URL. As with the county sites, the old URLs will still function.
The URL transition project required a good deal of link changes, which we automated to the best of our ability. If you experience any issues with a web tool and logging out does not help, or if your website is not behaving normally, please contact Dave Krause at djkrause@ucanr.edu.
- Author: Karl Krist
Hello ANR Colleagues!
For many of you this is the first email you are receiving from the ANR Internal Notifications System. I would like to explain this system to you.
The purpose of this system is to provide a single stream of important information for all ANR employees. This stream will be tailored to each individual based on who you are, and the jobs you perform.
This information is gathered from ANR blogs. Some blogs have been labeled as 'important' - meaning they will be viewed by everyone.
The blogs currently displayed to the entire Division are:
- ANR Report - News throughout ANR
- ANR Update - Important internal announcements
- CS&IT Updates - Important information from CS&IT (Including this message)
- Program Support Unit Updates - Information regarding Strategic Initiatives and events
If you own a blog that you feel should be distributed to the entire Division, please contact Karl Krist for inclusion in this system. If you have a blog that is important to PART of the Division, you can encourage people to add your blog to their feed.
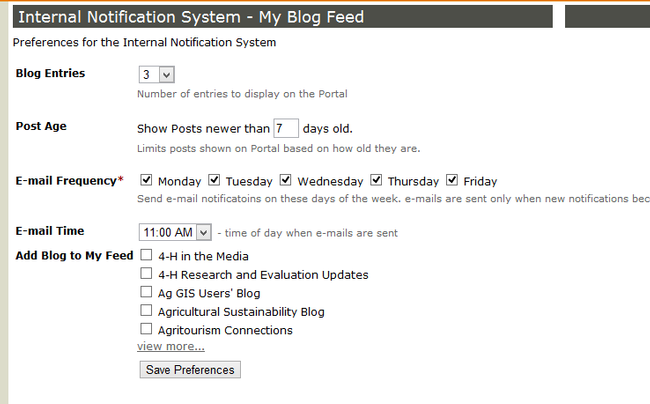
You can tailor which blogs are part of your own feed, and how often you are notified from within the ANR Portal. From the Portal click on the 'Manage My Feed' link. The next page gives you options on how many posts to display, how old posts should be before they automatically drop off, how frequently to receive email, and which blogs are part of your feed.
Soon, additional blogs will be added automatically to your feed based on a match from the Taxonomy system or unit roles. This feature will be implemented in the coming months.
As always, I welcome any feedback you have regarding this system. As this is the first time most of you are receiving this email, I am expecting a deluge of suggestions...and a few grumbles. All feedback is appreciated! Bonus points for feedback posted through the blog system.
Karl Krist
- Author: Karl Krist
I put the following blog article out a while ago, but in recent months we have had a deluge of phishing attempts. This is especially confusing for many users as a result of our move to Microsoft Exchange.
The post below is still applicable, but I can sum up the entire point in one easy statement:
Never give your password to anyone. Only use it to login to trusted sites. If the domain of the site is not what you are expecting (Not ucdavis.edu or ucanr.edu) then there is a good chance this is an attempt to trick you into giving up your credentials.
Please read on for a little more information.
Phishing...that is the name given to different types of 'social engineering' schemes to convince you to release information to some unsavory character, who will use it in unsavory ways.
Most of us are targets of phishing almost every day. We see much of this as email spam, and throw it away. Many of these scams are obvious- but some go well beyond trolling for neophytes, and they've fooled even the most jaded internet user.
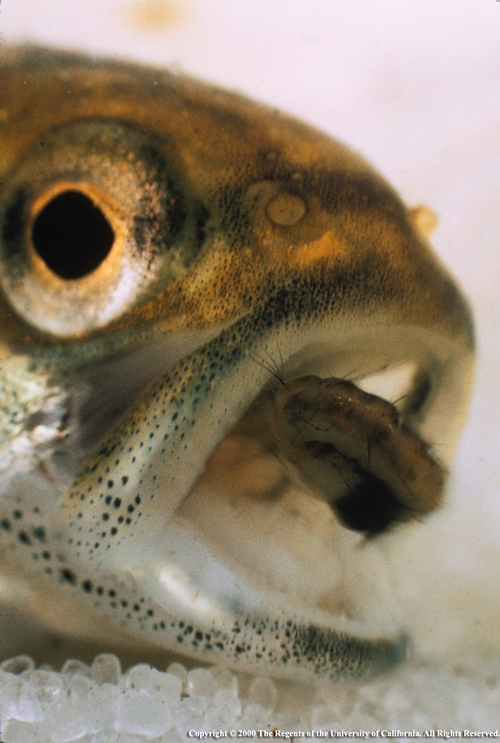
There's always a victim somewhere
I will tell you though, there are easy ways to avoid falling for phishing scams:
- Do not follow links sent in an email. You will be much better off typing in the main URL to the website, then navigating to function you need. For instance, if Wells Fargo asks you to update your personal information, type 'wellsfargo.com' into your browser, and login there and follow the directions. This way you know you will be safe.
- If you ignore rule #1, then please follow this rule! Always check the target of any link before you click on it. You can do this by hovering your mouse over the link- the real URL will be displayed in a little pop-up. Make sure it matches the link you *think* you will be going to. And please, please, please, make sure the link makes some sense! Recently someone sent me an email with links to '123contactform.com' - which was supposedly a way to update their UC Davis account information. NO! We would never send you to 123contactform.com! We would send you to a ucdavis.edu or ucanr.org domain.
- Think about what is being asked of you. Would your bank really send you an email asking you to update your social security number? No. If you doubt the legitimacy of a request- call the requestor!
Think before you link.

Turn the tables on phishing in 3 easy steps.
- Author: Michael L. Poe

The event took place in a tent at the steps of the California State Capitol and was presented by the UC Office of the President.
Time and location: April 30, 2012, 11am-3pm, West Lawn of the California Capitol Building, Sacramento.
Photos feature:
- Barbara Allen-Diaz
- Dan Dooley
- Rose Hayden-Smith
- Linda Katehi
- Abraham Lincoln (!)
- Carol Liu
- Craig McNamara
- Patt Morrison
- Lawrence Pitts
- Karen Ross
- Larry Smarr
- Timothy White
- Mark Yudof
- and the location, audience and select moments
Searches can be made on any of the individual names or for a look at all of the photos for the event, search for Morrill Act.
Of technical interest, 10 of the photos came from HD video. The native resolution is about 2000x1000 pixels. That could potentially make a decent professional print around 6x3 inches. The stills photos from HD video still need to be color-corrected and adjusted for use (we've done this already for the images we just added to the Repository) but this opens up exciting print possibilities we haven't had before with video images.